Computers & Technology
epub |eng | 2019-05-29 | Author:Stephen Samuel [Stephen Samuel]
@JvmName Due to erasure in the JVM, it is impossible to declare two functions with the same name and the same erased signature. For example, the following declarations in Java ...
( Category:
Programming & App Development
May 24,2020 )
epub |eng | | Author:Jason Strate
Defragmentation Strategies So far we’ve discussed how fragmentation occurs, why it is an issue, and how it can be removed from indexes. It is important to apply this knowledge to ...
( Category:
SQL Server
May 24,2020 )
epub |eng | 2019-03-31 | Author:Eric Meadows-Jonsson & Darin Wilson [Eric Meadows-Jonsson]
( Category:
Mobile App Development & Programming
May 24,2020 )
epub |eng | 2019-05-22 | Author:Unknown
Figure 10.1 The limit cycle of the Hicks model, for two different values of the accelerator coefficient v, namely, v = 1.5 and v = 3.0. National income Y(t) is ...
( Category:
Memoirs
May 23,2020 )
azw3 |eng | 2015-06-28 | Author:Spencer, Lawrence & Richards, Seth [Spencer, Lawrence]
WROX.COM CODE DOWNLOADS FOR THIS CHAPTER You can find the wrox.com code downloads for this chapter at www.wrox.com/go/reliablejavascript on the Download Code tab. The files are in the Chapter 13 ...
( Category:
Programming
May 23,2020 )
azw3 |eng | 2015-06-28 | Author:Lawrence Spencer & Seth Richards [Spencer, Lawrence]
WROX.COM CODE DOWNLOADS FOR THIS CHAPTER You can find the wrox.com code downloads for this chapter at www.wrox.com/go/reliablejavascript on the Download Code tab. The files are in the Chapter 13 ...
( Category:
Programming
May 23,2020 )
epub |eng | 2019-01-24 | Author:Unknown
159 CHAPTER 7 DATA CLASSIFICATION WITH DECISION TREES action is a string that is either “train” or “test.” d is the data structure that defines the tree. t are the ...
( Category:
Adventure
May 23,2020 )
epub |eng | 2018-12-26 | Author:Sion Retzkin [Sion Retzkin]
But, even with all its security, privacy, and anonymity options, Tails has weaknesses. For example (according to the Tails website documentation), note the following: Tails does not protect against compromised ...
( Category:
Networking & Cloud Computing
May 23,2020 )
epub |eng | 2018-11-30 | Author:Jordan Krause [Jordan Krause]
But I'm an IT guy, right? Don't you think I could find some way of circumnavigating this setting, even though my account only has regular user permissions? Nope, not that ...
( Category:
Windows Administration
May 23,2020 )
epub |eng | 2018-11-30 | Author:Prashanth Jayaram [Prashanth Jayaram]
This is what we did: We listed out the files to delete: we subtracted the LastWriteTime from today, and performed a Floor() operation on it since we were not allowed ...
( Category:
Linux & UNIX Administration
May 23,2020 )
epub |eng | 2018-12-31 | Author:Sebastiaan Tammer [Sebastiaan Tammer]
Summary This chapter explained regular expressions, and two common tools that use them under Linux: grep and sed. We began by explaining that regular expressions are search patterns, used in ...
( Category:
Linux & UNIX Administration
May 23,2020 )
epub |eng | 2018-10-30 | Author:Unknown
Chapter 5 List stories map(ids => ids.slice(offset, offset + limit)), mergeMap((ids: any[]) => combineLatest(...(ids.map (id => this.db.object('/v0/item/' + id).valueChanges())))), map((items: any) => ({ offset, limit, total: limit, results: items, })) ...
( Category:
Adventure
May 23,2020 )
epub |eng | | Author:Ecky Putrady
The parameters are similar to getMsg. The fourth parameter is the callback that will be invoked when we receive a message. The callback is simply an IO action that accepts ...
( Category:
Web Development & Design Programming
May 23,2020 )
epub, azw3 |eng | 2020-05-21 | Author:Lim, Greg [Lim, Greg]
So you see how you can extend your application with more validation checks? Implementing Custom Validation Exercise In the previous example, we illustrated how to add custom validation capabilities to ...
( Category:
Programming
May 23,2020 )
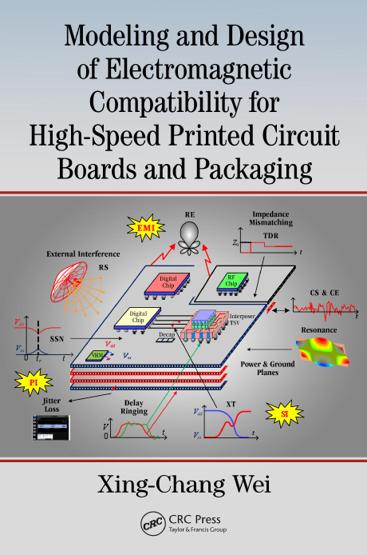
epub, pdf |eng | 2017-03-16 | Author:Xing-Chang Wei [Wei, Xing-Chang]
Integral Equation Solutions ◾ 155 0.5 Via 1 1.8 | Y Results by using the software HFSS 11| by using the software HFSS 0.4 | Y Results by using the ...
( Category:
Hardware & DIY
May 23,2020 )
Categories
Popular ebooks
Deep Learning with Python by François Chollet(27919)The Mikado Method by Ola Ellnestam Daniel Brolund(25224)
Hello! Python by Anthony Briggs(24261)
Secrets of the JavaScript Ninja by John Resig Bear Bibeault(23351)
Kotlin in Action by Dmitry Jemerov(22435)
The Well-Grounded Java Developer by Benjamin J. Evans Martijn Verburg(21900)
Dependency Injection in .NET by Mark Seemann(21785)
OCA Java SE 8 Programmer I Certification Guide by Mala Gupta(20646)
Algorithms of the Intelligent Web by Haralambos Marmanis;Dmitry Babenko(19476)
Grails in Action by Glen Smith Peter Ledbrook(18549)
Adobe Camera Raw For Digital Photographers Only by Rob Sheppard(17020)
Sass and Compass in Action by Wynn Netherland Nathan Weizenbaum Chris Eppstein Brandon Mathis(15810)
Secrets of the JavaScript Ninja by John Resig & Bear Bibeault(13660)
Test-Driven iOS Development with Swift 4 by Dominik Hauser(11806)
Jquery UI in Action : Master the concepts Of Jquery UI: A Step By Step Approach by ANMOL GOYAL(11133)
A Developer's Guide to Building Resilient Cloud Applications with Azure by Hamida Rebai Trabelsi(10618)
Hit Refresh by Satya Nadella(9175)
The Kubernetes Operator Framework Book by Michael Dame(8559)
Exploring Deepfakes by Bryan Lyon and Matt Tora(8396)
Robo-Advisor with Python by Aki Ranin(8340)